Introduction
Cybersecurity readiness has become a critical factor for companies expanding into Southeast Asia. Many businesses begin regional growth by focusing on market entry, hiring, and setting up local operations. However, as they grow across multiple countries, the operating model becomes more complex, with different systems, vendors, and regulatory requirements to manage simultaneously, increasing overall cyber risk.
As a result, security gaps begin to appear. Controls may be inconsistent, and system visibility becomes fragmented. Local data regulations are not always aligned. Over time, these issues can lead to operational disruption, partnership delays, or compliance risks.
In this guide, we – Source of Asia, explain what cyber readiness means in a regional context, where these risks typically arise, and how to assess and strengthen your setup to support stable, compliant growth across ASEAN markets.
Key Insights
- Cybersecurity readiness determines whether companies can scale safely across multiple ASEAN markets.
- Expansion increases cyber risk exposure through systems, users, and third-party vendor dependencies.
- Weak cybersecurity slows growth by delaying deals, disrupting operations, and blocking market entry.
- Regulatory differences across ASEAN require localized compliance and continuous security alignment.
- A structured readiness model improves resilience through governance, controls, and response capability.
What Cybersecurity Readiness Really Means for Expanding Companies
Most companies assume their systems are secure until something goes wrong, such as a failed login, system outage, or unusual data access. At that point, the issue is not just the incident itself, but whether the business can respond without disrupting operations.
This is why cyber readiness matters. It reflects the ability to detect, identify, and respond to threats in a structured way, supported by clear processes and tested response plans. This includes controlling access to systems and data, detecting issues early, responding quickly with defined actions, and recovering operations with minimal disruption, which defines effective cyber readiness in practice.
As operations expand across markets, this capability supports business continuity, not just IT. Incidents can disrupt sales, delay partnerships, and affect daily activities. A well-prepared setup helps maintain stable operations and reduces downtime during expansion.
To manage this at scale, companies rely on three core pillars:
- Governance: establishes ownership, policies, and decision-making across markets.
- Controls: implement safeguards, including access control, monitoring, and data protection.
- Response capability: ensures the business can detect, contain, and recover from incidents.
It is also important to distinguish cyber readiness from compliance:
- Compliance focuses on meeting required regulations and passing audits.
- Readiness focuses on the ability to operate safely during real incidents.
As companies expand into new markets, relying solely on compliance often creates gaps. A readiness-based approach provides the level of control needed to operate under varying risk conditions.
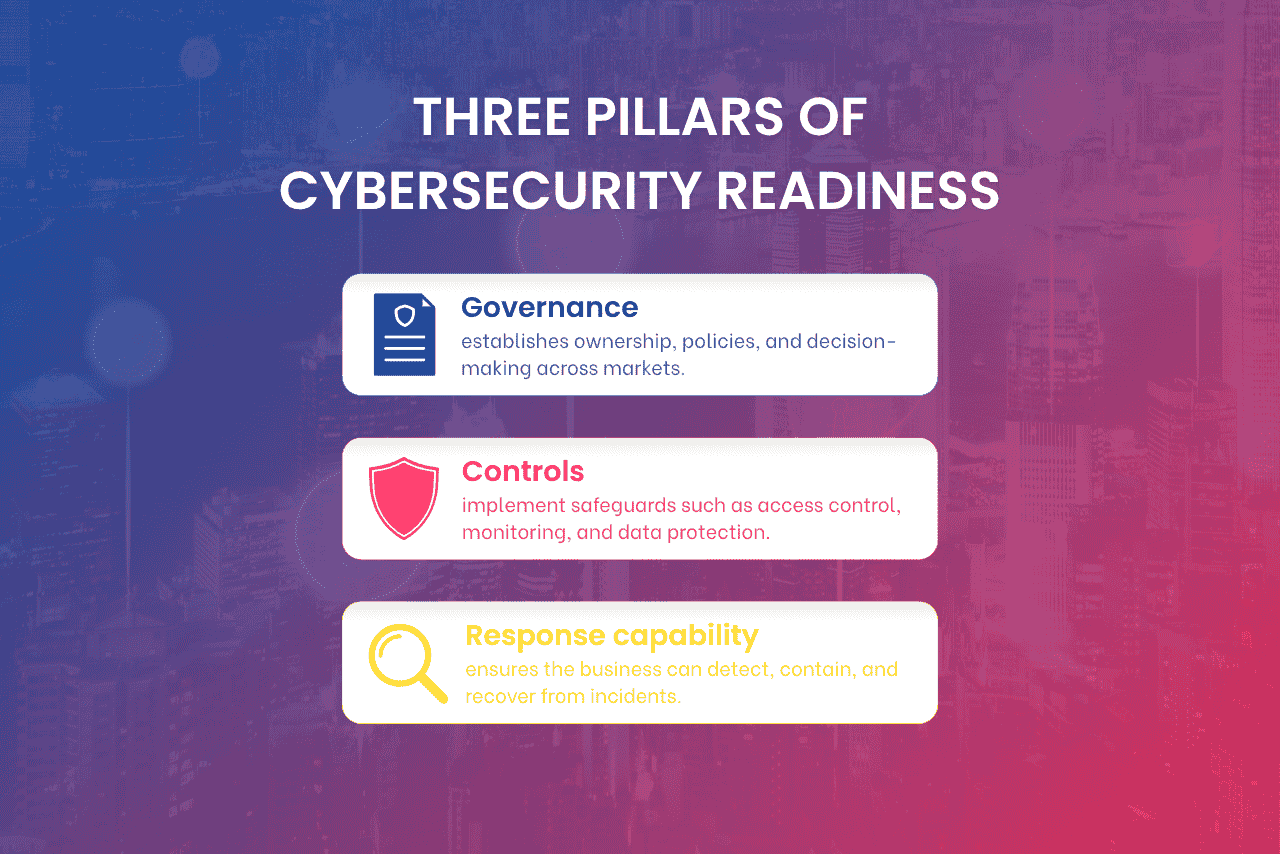
Three pillars of cybersecurity readiness, including governance controls and response capability for business expansion.
Why Cybersecurity Readiness Is Critical for Regional Expansion
Expansion into new markets increases cyber exposure, introduces different regulatory requirements, and makes cyber readiness a key factor in enterprise trust and deal execution.
Expansion increases exposure to cyber risks
As companies expand across markets, their attack surface increases, which directly raises the risk of cyber attacks. For example, entering a new country often involves setting up new systems, granting access to local teams, and working with external vendors. Each of these creates new entry points that attackers can target.
This risk typically grows through:
- More systems and platforms: Inconsistent setup or missed updates can expose vulnerabilities
- More users across locations: Weak passwords or improper access can lead to unauthorized entry
- More third-party vendors: A vendor with weaker security can become an indirect access point
Regulatory differences create compliance challenges
As companies expand across Southeast Asia, cybersecurity and data protection laws vary by country, creating a fragmented compliance landscape. For instance, Singapore’s PDPA requires strict data governance and breach reporting. Vietnam’s Cybersecurity Law may impose local data storage obligations for qualifying services and data categories. Meanwhile, Indonesia may require local storage or local processing for certain regulated data categories.
These differences lead to some key challenges, including that requirements are not aligned across markets, enforcement levels vary, and cross-border data transfers often need extra approvals or system changes. Without preparation, companies risk missing local obligations, which can slow expansion and increase compliance exposure.
Security gaps can slow down growth
When companies expand into new markets, cybersecurity gaps often appear during key commercial stages, such as enterprise negotiations, vendor onboarding, or pre-launch reviews. At this stage, security becomes part of how external partners judge business reliability, not just an internal IT issue.
This impact typically shows in three ways:
- Enterprise clients require security due diligence, reviewing systems, access control, and data handling before approving contracts.
- Weak controls reduce trust in partnerships, especially when governance or response processes are unclear or inconsistent.
- Operational risks delay market entry when security assessments or remediation work must be completed before go-live.
| 👉 Cybersecurity readiness becomes more critical as companies move into new ASEAN markets. Learn how market expansion works in this region. |
Key Cyber Risks in ASEAN Operations
Cyber risks in ASEAN are driven by rapid digital adoption, uneven security maturity, and increasing reliance on interconnected systems. As operations scale across markets, these risks become harder to manage consistently.
The following are the key cybersecurity risks companies typically face when operating across ASEAN:
- Lack of centralized visibility across markets. Fragmented systems and reporting limit real-time monitoring. This reduces the ability to identify and respond to threats across subsidiaries.
- Identity and access vulnerabilities. Weak authentication, excessive access rights, and a lack of centralized identity control increase the risk of unauthorized access and credential-based attacks.
- Third-party and vendor risks. Vendors often operate with lower security standards. Limited visibility into their practices makes the supply chain a common entry point for attacks.
- Cloud and system misconfigurations. Inconsistent configurations across markets can expose systems unintentionally. Misconfigurations remain a leading cause of security incidents.
- Cross-border data and compliance challenges. Different requirements for data storage, transfer, and privacy create complexity and increase the risk of non-compliance.
- Growing threat exposure and operational gaps. Increasing ransomware, phishing, and supply chain attacks are combined with internal constraints such as limited security talent and legacy systems. According to IBM Cost of a Data Breach benchmarks, the average cost of a data breach in the region is estimated at US$3.67 million, reflecting the operational and financial impact of these risks.
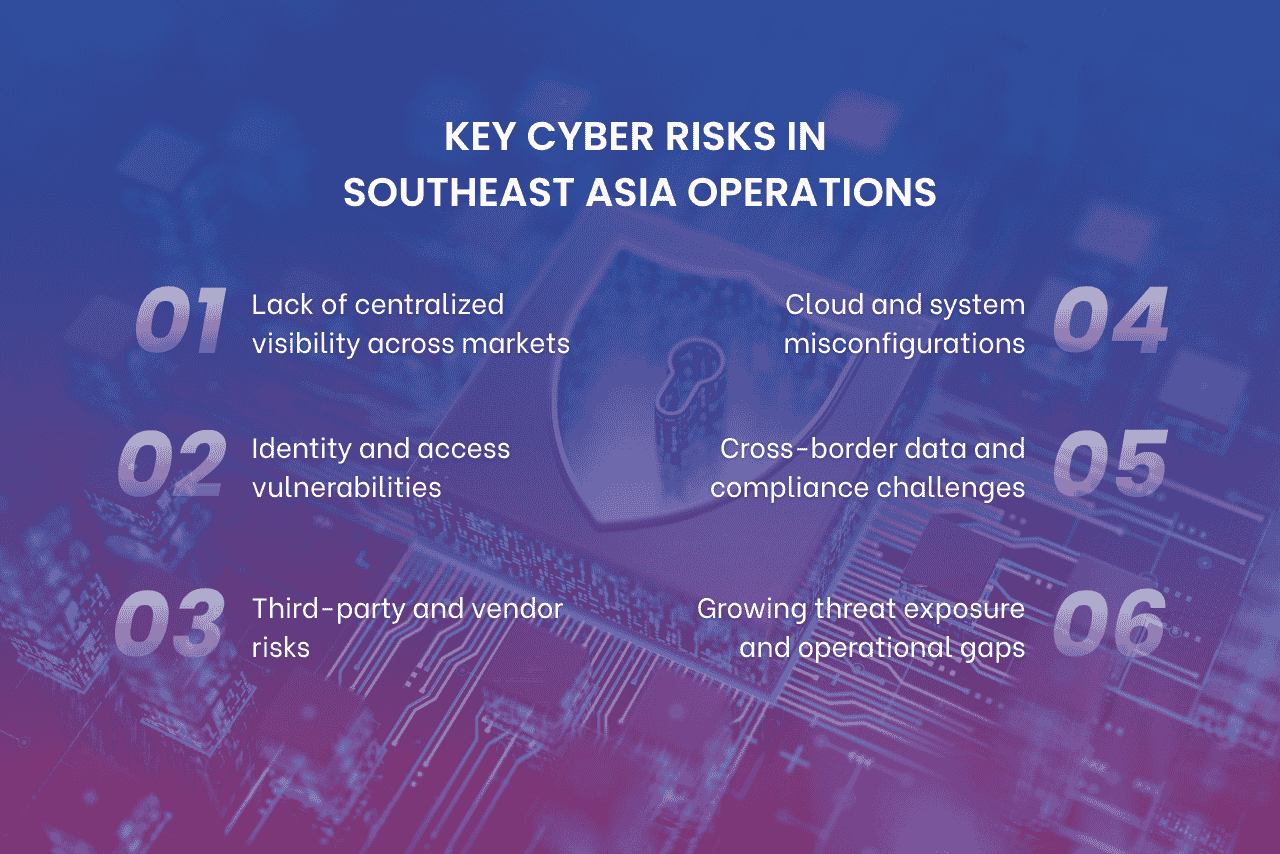
Key cybersecurity risks in ASEAN include ransomware, phishing, vendor, and cloud misconfiguration risks across markets.
Cybersecurity Realities Across Key ASEAN Markets
Cybersecurity maturity across Southeast Asia varies by market, driven by different regulatory frameworks, digital adoption levels, and enforcement capacity. As a result, companies need to align with local conditions, not apply a single regional approach.
| Market (*) | Key Characteristics |
| Singapore | High maturity with strong regulation and enforcement. Companies must meet strict standards on governance, reporting, and critical infrastructure protection. |
| Vietnam | Rapid digital growth with evolving regulations. Increased focus on data control and localization creates both compliance pressure and operational challenges. |
| Indonesia | Large-scale digital economy with decentralized systems. The Personal Data Protection Law (2022) strengthens compliance, but operational complexity remains high. |
| Thailand | Industry-specific requirements, especially in regulated sectors. Cybersecurity maturity varies, requiring tailored approaches by industry. |
| Malaysia | Strengthening the regulatory framework under the Cyber Security Act 2024, with clearer requirements for incident reporting and audits. |
| Philippines | Developing infrastructure with rising digital adoption. Higher exposure to cyber threats requires improved monitoring and risk control. |
(*) Maturity levels vary by sector and company size.
| Cyber readiness is closely tied to how each market develops its digital ecosystem and regulatory maturity.
👉 Explore the regional tech positioning of Vietnam, Singapore, and Malaysia as technology hubs in ASEAN. |
How To Evaluate Your Cybersecurity Readiness Before Scaling
A structured cyber readiness assessment helps identify operational and technical gaps before expansion. Many companies also combine this with a cybersecurity maturity assessment to benchmark current capabilities and prioritize investments. The evaluation should focus on five key areas:
Governance and control maturity
Start by assessing whether security ownership and decision-making are clearly defined. This includes reviewing internal policies, assigning accountability, and escalation processes during incidents. You should also check if governance is applied consistently across all markets. Without a clear structure, decisions become fragmented, especially in multi-country operations.
Technical readiness
Next, evaluate how well your systems are secured in daily operations. This includes patch management, system monitoring, access control, and data protection mechanisms. It is also important to verify whether backups are reliable and regularly tested. A strong technical baseline reduces exposure to known vulnerabilities and misconfigurations. This is often one of the first areas reviewed when organizations ask how to enhance cybersecurity readiness before entering multiple ASEAN markets.
Response capability
Then, assess how effectively your organization can detect, respond to, and recover from incidents. This involves reviewing detection tools, response procedures, and defined roles during incidents. Testing response plans through simulations is critical to ensure the business can recover quickly with minimal disruption.
Third-party resilience
Expansion increases reliance on vendors, so you need to evaluate third-party security posture. This includes vendor risk assessments, contractual security requirements, and ongoing monitoring of vendor access. Many breaches originate from weaker third-party controls, making this a key risk area.
Regional compliance readiness
Finally, verify your ability to meet local cybersecurity and data regulations. This includes understanding country-specific laws, managing data protection requirements, and handling cross-border data flows correctly. Misalignment here can delay operations and increase regulatory risk.
A combined cybersecurity maturity assessment and regulatory review helps identify gaps, prioritize risks, and build a practical roadmap for secure expansion.
A structured cybersecurity readiness assessment evaluates governance, systems, response capability, vendors, and compliance before scaling into new markets.
How Weak Cybersecurity Slows Expansion
Weak cybersecurity readiness creates direct barriers to expansion by affecting deal execution, operations, compliance, and market trust. Instead of supporting growth, security gaps often introduce delays, added costs, and reputational risk.
Security concerns delay enterprise partnerships and commercial deals
In expansion stages, security becomes part of commercial evaluation, not just an internal function. Enterprise clients increasingly require a clear and verifiable security posture before moving forward. As a result, vendor due diligence processes now go deeper into how systems, data, and access are managed. This often includes reviewing:
- Data handling practices and protection measures
- Access control and identity management
- Incident response and recovery capability
When these areas are unclear or underdeveloped, confidence is reduced. Consequently, companies may face longer approval cycles, additional remediation requests, or even lost deal opportunities.
Operational incidents interrupt scaling plans
Security incidents have a direct impact on daily operations, especially during critical expansion phases. For example, system downtime can delay rollout activities, disrupt integrations, or pause operations in new markets. As a result, expansion timelines become harder to control.
At the same time, internal teams are often forced to shift focus from growth initiatives to incident response and system recovery. This creates resource strain and slows execution. Over time, repeated disruptions can also affect performance, with some businesses experiencing measurable revenue impact due to operational instability.
Compliance gaps create regulatory friction and market-entry delays
Expanding across markets requires alignment with local cybersecurity and data regulations, which often differ by country. When compliance is not fully addressed, it can slow down or even block market entry.
For example, Vietnam’s data localization requirements or Indonesia’s data storage rules may require system changes before operations can begin. In practice, gaps often lead to the following:
- Licensing delays due to incomplete regulatory alignment
- Unmet data protection requirements, requiring additional remediation
- Restrictions on cross-border data flows affect system design
Thus, operational setup is delayed, and expansion timelines become less predictable.
Reputation damage weakens new market traction
In new markets, trust is a key factor for early growth. However, security incidents can quickly reduce confidence among customers, partners, and regulators. Once concerns around data protection or system reliability arise, companies often face higher scrutiny and slower engagement.
As a result, credibility becomes harder to build, slowing customer acquisition and partnerships. Over time, repeated incidents weaken brand perception, making it more difficult to compete and sustain both short-term traction and long-term positioning.
To bring these impacts together, the table below summarizes how weak cybersecurity affects key areas of expansion.
| Expansion Area | Impact of Weak Security |
| New Market Entry | Regulatory penalties and loss of trust in new regions |
| Digital Transformation | Delays in cloud or AI adoption due to security concerns |
| Partnerships / M&A | Third-party vulnerabilities are slowing or blocking deals |
| Hiring / Scaling | Increased insider risks, both accidental and intentional |
Conclusion
Cyber risk is unavoidable in expansion and without readiness because it increases operational disruption and compliance exposure. As companies scale across ASEAN, growing system complexity and regulatory differences make risk management harder. A structured cybersecurity approach strengthens governance, controls, and response capability to support stable and sustainable growth.
In Southeast Asia, readiness also depends on local regulatory understanding and execution. Before entering new ASEAN markets, it is important to assess whether your systems, vendors, and governance can scale securely. Understanding this, Source of Asia helps companies align market expansion with operational and cybersecurity readiness across Southeast Asia.
| 👉 Get in touch with us to assess your cybersecurity readiness and prepare for potential cyber risks. |
Frequently Asked Questions
Companies assess cybersecurity readiness through risk assessments, asset and system audits, policy and compliance reviews, incident response testing, and third-party risk checks. This helps ensure security controls, governance, and response capability can scale safely with business growth.
Key risks include ransomware, phishing, weak patching, insecure system configurations, and third-party vulnerabilities. These are intensified by rapid digital adoption, uneven security maturity, limited cyber talent, and fragmented regulatory environments across ASEAN.
Weak cybersecurity can disrupt operations, increase recovery costs, and trigger regulatory penalties. It also reduces trust from clients and partners, which can delay or block market entry, partnerships, and digital expansion initiatives.
Yes. Local support is important due to country-specific regulations, reporting rules, and threat environments. Local experts help improve compliance, speed up incident response, and align cybersecurity practices with each market’s operational realities.